Learn how to get more out of Beamo with Plans and Packs.
Introduction
This article details the necessary steps for using Beamo's SAML SSO with Okta as the Identity Provider.
Who can use this feature?
| Super Admin | Site Manager | Team Admin | Surveyor | Collab- orator |
Viewer | |
| Setup SAML SSO |
Setting up SAML SSO
Open SSO in Beamo
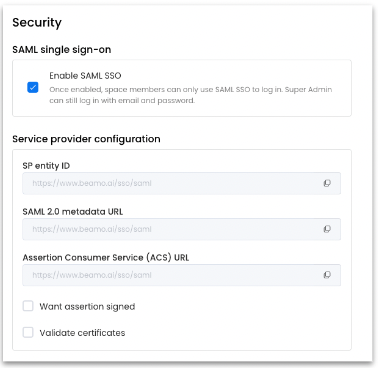
The SSO configuration is located in the Settings of Beamo.
- Beamo → Settings → Security
Click “Enable SAML SSO” to start the process.
Create an Okta App
Note: Providers’ configuration instructions are outlined here. For more detailed configuration instructions, please contact the respective ID provider.
- Open the Okta Admin Portal and navigate to the Applications.
- Click Add Application and create a new application with Create New App.
- Select Web from the dropdown and select SAML 2.0.
- Click Create and continue to the configuration part.
- Give the application a Name, e.g. Beamo on the General Settings.
- Go to the section Configure SAML.
Configure the following fields:
| Field | Description |
|
Single sign on URL |
Set this field to the pre-generated Assertion Consumer Service (ACS) URL retrieved from the Beamo SSO configuration screen. |
|
Audience URI (SP Entity ID) |
Set this field to the pre-generated SP Entity ID retrieved from the Beamo SSO Configuration screen. |
|
Name ID format |
(Optional) Select the SAML Name ID format to use in SAML assertions. By default, this field is Unspecified. |
|
Application username |
Select the Okta attribute users will use to log in to Beamo. |
Attribute mapping
Go to the Show Advanced Settings link. In the Attribute Statements section, create the following SP → IdP mapping:
| Name | Name format | Value |
|
|
Unspecified |
user.email |
Assignments
Go to the Assignments tab and assign access to the application on a user-by-user basis using the Assign to People option or in-bulk using the Assign to Groups option.
Setup Instructions
Select the Sign On tab for the app and select the [View Setup Instructions] button. Take note of the:
- Identity Provider Single Sign-On URL
- Identity Provider Issuer
- Download the X.509 Certificate
Continue on to Beamo
The Okta Admin Portal-specific configurations are done. Continue on to Beamo to finish the configuration.
- Service Provider Configuration defines the format of SAML requests.
- Identity Provider Configuration defines the format to expect for SAML responses.
Service Provider Configuration
Configure the following fields according to the choices selected in the Okta Admin Portal during setup:
| Field | Description |
|
Want Assertions Signed |
Condition where Beamo expects SAML assertions to be signed. |
|
Validate Certificates |
Check this box when using trusted and valid certificates from your IdP through a trusted CA. |
Identity Provider details
Identity Provider Configuration will often require you to refer back to the Okta Admin Portal to retrieve application values:
| Field | Description |
|
Entity ID |
Enter the Identity Provider Issuer retrieved from the Okta Sign On Settings. |
|
Single Sign On Service URL |
Enter your Identity Provider Single Sign-On URL retrieved from the Okta Sign On Settings screen. |
|
X509 Public Certificate |
Paste the retrieved Certificate, removing -----BEGIN CERTIFICATE----- and -----END CERTIFICATE-----. Extra spaces, carriage returns, and other extraneous characters will cause certification validation to fail. |
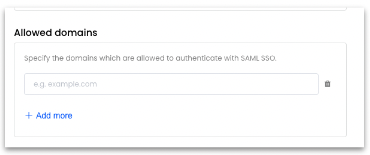
Allowed domains
Specify the email domains which are allowed to authenticate with SAML SSO. Add one domain per field. If the users log in with name@example.com, the domain to be entered is example.com.
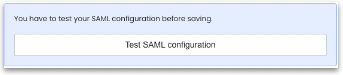
Test & Save
After the tests are successful, [Save] the configuration, and SSO will be enabled.